DMARC: Four Years of Enhancing Email Security - A Look Back and Forward
2015/11/02 by Jérôme Gays.
 It has been almost 4 years since the DMARC procedures were first launched, as well as our first publication of an article regarding this topic. As a reminder, DMARC is a Spoofing-fighting validation system. It relies on technologies such as SPF and DKIM, empowering email senders to provide receivers servers with the procedures of what actions are to be deployed if authentication has not been achieved. It allows the original sender to remain updated about any failure occurring during the SPF and DKIM authentication mechanisms.
It has been almost 4 years since the DMARC procedures were first launched, as well as our first publication of an article regarding this topic. As a reminder, DMARC is a Spoofing-fighting validation system. It relies on technologies such as SPF and DKIM, empowering email senders to provide receivers servers with the procedures of what actions are to be deployed if authentication has not been achieved. It allows the original sender to remain updated about any failure occurring during the SPF and DKIM authentication mechanisms.
If you want to know the technical details about the DMARC mechanism, please read our article dating back to 2012.
DMARC DEPLOYED BY ISPS.
Before talking about advertisers’ techniques, we will aim to explain how do ISPs and Webmails operate. This can be split into 2 major problematics.
On one hand, we find DMARC deployment on ISPs and Webmails outgoing emails. In April 2014, Yahoo! published the ‘Reject Policy’ (p=reject), through which it will reject any mail from @yahoo.com if it came from a non-authored SMTP server.
This was a rather harsh measure, specially if we consider that plenty of yahoo.com users used to send emails from other email servers such as Outlook or Thunderbird, using their ISP’s SMTP connectors. In the same manner, the great deal of minor advertisers sending their newsletters through a routing platform, were no longer enabled to use a @yahoo.com.-address. A few days later, AOL and many others continued to follow this path.
Here below a brief analyze of the most representative domains in France:
> Gmail.com – v=DMARC1; p=none; rua=mailto:mailauth-reports@google.com – No reject policy, however it implements an error monitoring strategy.
> Hotmail.com – v=DMARC1; p=none; pct=100; rua=mailto:d@rua.agari.com; ruf=mailto:d@ruf.agari.com; fo=1 – No reject policy, however it implements an error monitoring strategy.
> Orange.fr – No DMARC records.
> Sfr.fr – No DMARC records.
> Free.fr – No DMARC records.
> LaPoste.net – v=DMARC1; p=quarantine; rua=mailto:dmarc.agg@laposte.net,mailto:dmarc_agg@auth.returnpath.net; ruf=mailto:dmarc.afrf@laposte.net,mailto:dmarc_afrf@auth.returnpath.net; rf=afrf; – Error quarantine and monitoring.
The hard works comes when it comes to determine DMARC management. For instance, it comes to evidence to think that the PayPal domain would request for a reject policy. However it would be also necessary that ISPs and Webmails receiving scam emails duly comply to PayPal procedures, leading to a final rejection of these emails.
Here below a list of what we currently know about the beforesaid ISPs:
> Gmail : Emails are properly filtered according to the DMARC machanisms.
> Hotmail/Outlook.com : Emails are properly filtered according to DMARC machanisms.
> Orange : No actions are deployed.
> SFR : No actions are deployed.
> Free : No actions are deployed.
> LaPoste.net : No actions are deployed.
According to this, it comes to evidence that the French market has been quite neglected — it is impossible to claim that the major open-public sending servers have the cutting-edge technologies. Work has not been relevant, other that the actions deployed at LaPoste.net.
UNIVERSALLY ACCEPTED BY ADVERTISERS?
Among the enterprises deploying DMARC mechanisms we may find Bank of America, JPMorganChase, PayPal, LinkedIn and Facebook, the social medias and finances big boys who are often victims of Spoofing and Phishing.
So, what about France? Are public institutions operating properly? (who had never received an email signed on behalf of the CAF or the Tax Department offering money refunds). Have the major financial institutions taken actions to improve risk-management measures?
To sum up, here below a list of the institutions put under the spotlight:
> Crédit Agricole – No DMARC record.
> Ameli.fr – No DMARC record.
> CAF.fr – No DMARC record.
> Impots.gouv.fr – No DMARC record (nor on the gouv.fr domain).
> Caisse-epargne.fr : No DMARC record.
> Societegenerale.fr – DMARC record in ‘none’ policy.
> bnpparibas.com – No DMARC record.
We analyzed a great deal of domain names, however, it was sadly within the public institutions or within the banking-insurance arena that we found few domains protected.
With this in mind, the one possible question is if these major institutions — which are easy-target for phishing — are aware of their vulnerable situation? On the other hand, ISPs are also highly vulnerable to phishing. However, being aware of this condition, very little has been done to implement DMARC mechanisms.
Implementation is a rather simple though. If the deployment of quarantines and reject policies might seem quite scary, it is not always the first step to start with. Most enterprises implement firstly a ‘none’ policy in order to enable alert monitoring, and it is only after a several-week analyze that the good policy is finally set up.
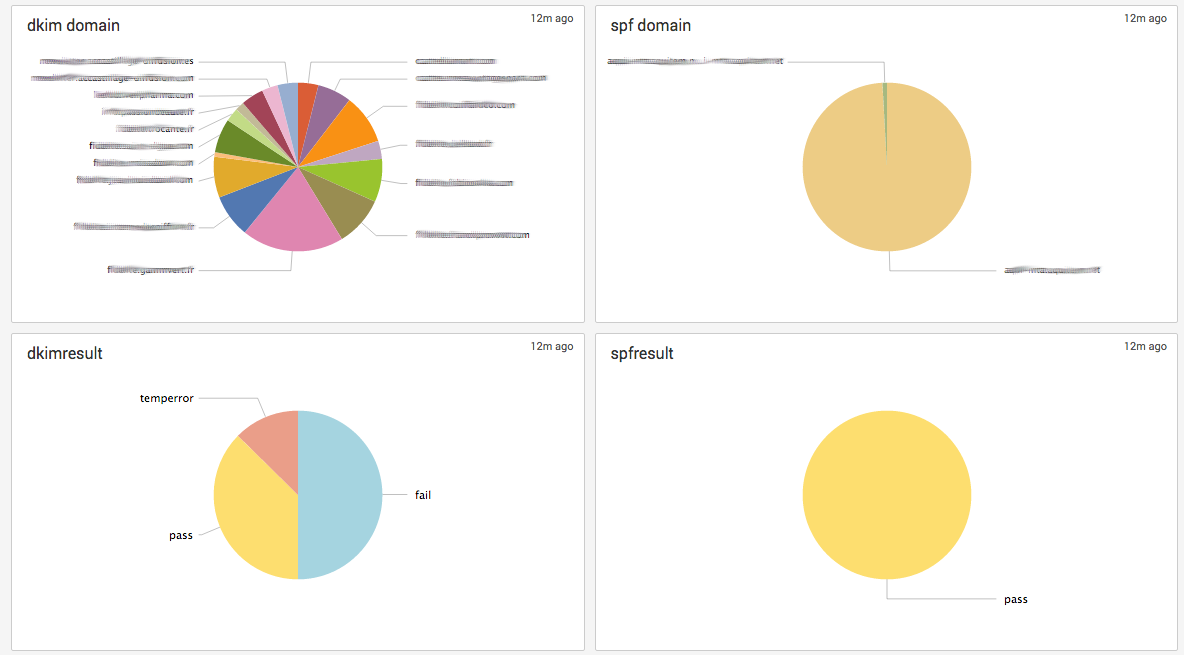
DeliverNow has implemented a DMARC-based email monitoring suite. In such way, error reports sent by providers are analyzed and rendered available on our deliverability dashboards. Hence, we receive data from IP addresses that are not authorized to send emails using our customer’s domain name. We are empowered thus to detect any upcoming authentication issue on legitimate emails. An alert system enhances real-time pop-up alerts of any relevant problem.
FEW OF THE LATEST UPDATES:
Within the framework of the 35th M³AAWG General Meeting, we were informed about the new DMARC mechanisms deployed by some operators including:
As of early November, Yahoo! will first start to extend its reject policy to the ymail.com and rocketmail.com, domains, before doing so to some other domains in the upcoming months.
Google has announced the implementation of a more stringent policy in order to protect its domains. Gmail should move towards a reject policy as of June 2016.
Here below an example of the DMARC procedure deployed by Postmastery’s deliverability monitoring suite.
If you need more information, please contact us via our contact form.